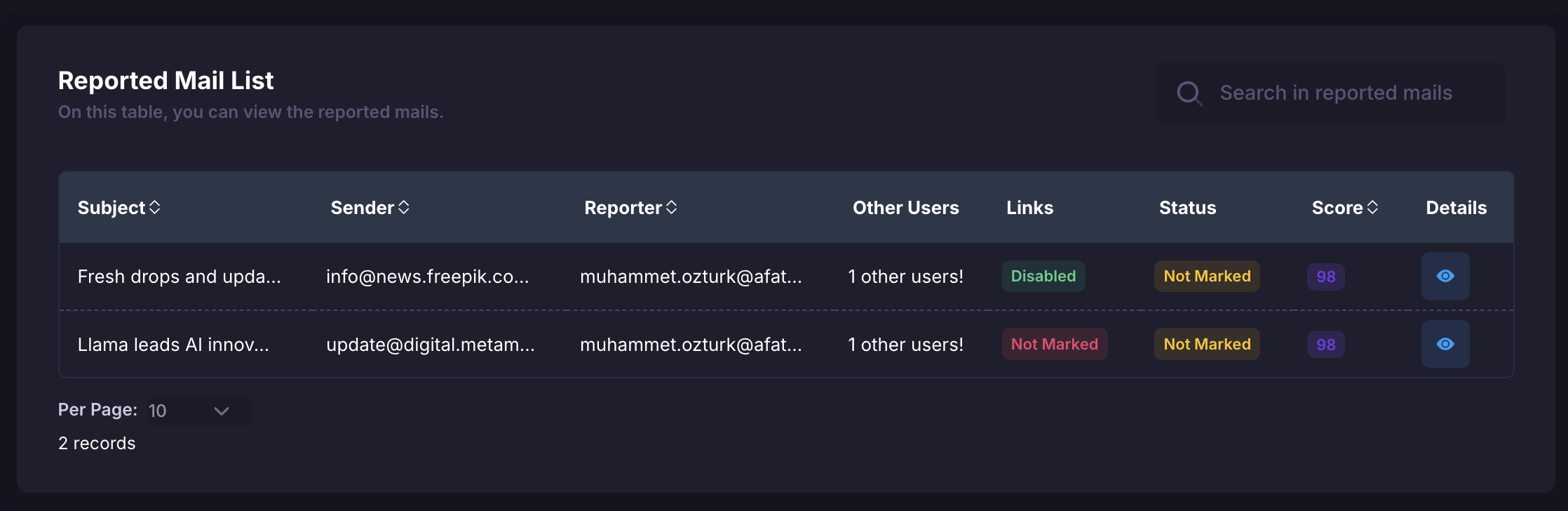
Users can report a suspicious email to the Phishy platform with a simple click of the button provided in the extension. Once reported, the email is automatically analyzed by the system, and the necessary security actions are taken and presented to you. By navigating to Incident Response > Reported Mails in the menu, you can view a page similar to the one below.Documentation Index
Fetch the complete documentation index at: https://docs.phishy.io/llms.txt
Use this file to discover all available pages before exploring further.
Reported Email Details
The reported email details display the security assessment or outcome of the email. For example, “Safe” indicates that the email poses no security threat or malicious content. You may also encounter other labels such as low risk, medium risk, or high risk. For instance, if the email is labeled as medium risk, you might see warnings like “No similarity found in name and email”, “The email subject contains potentially harmful words”, or “The email content contains spam words”. You can access more detailed risk information based on the risk status.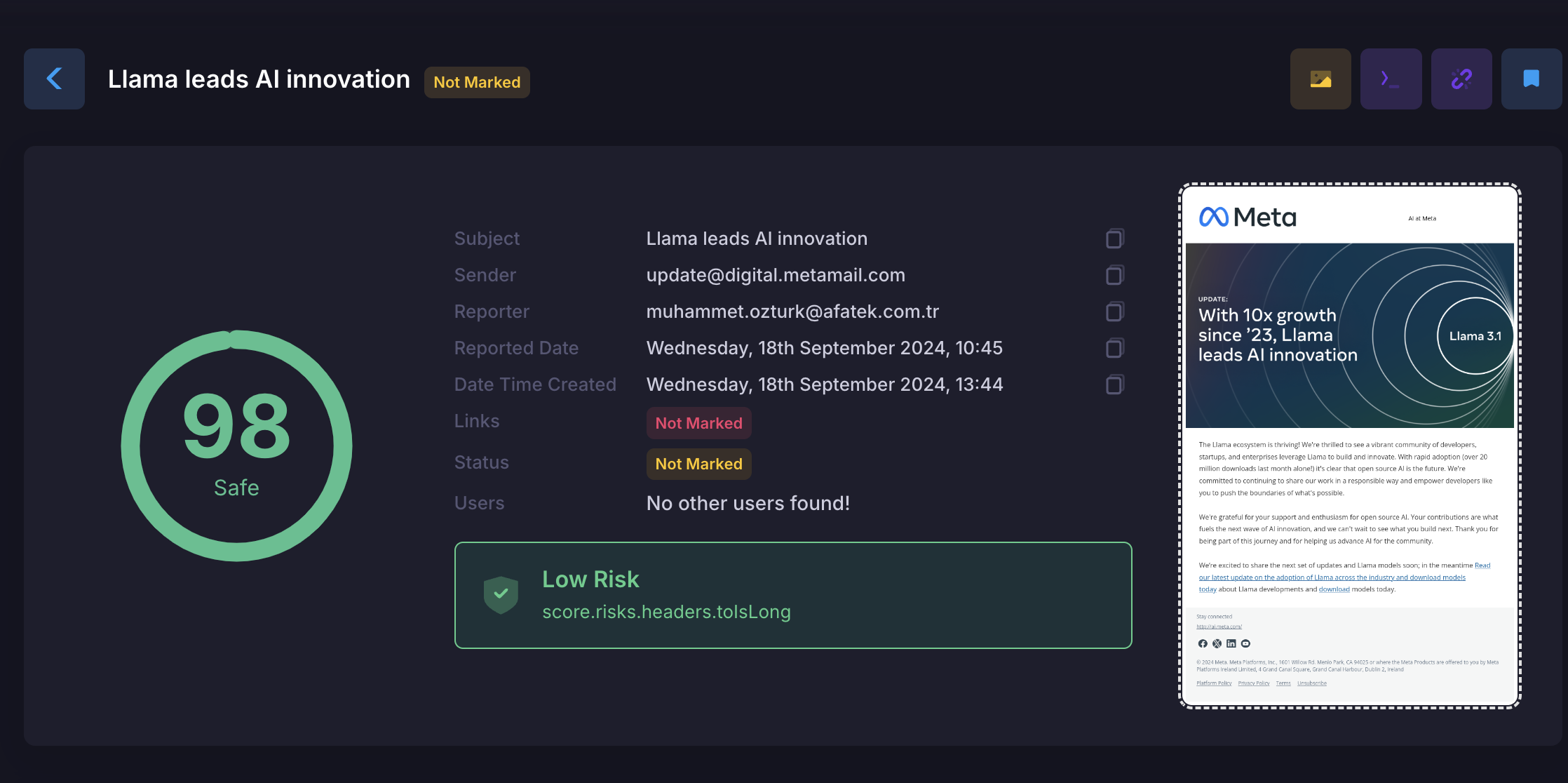
- 🔗Links (Enabled/Disabled): Lists the links present in the email. The security evaluation of each link and whether the link is present or not (Enabled/Disabled) is indicated.
- ✅ / ❌Status (Flagged/Unflagged): Shows the status of the email. For example, if “Not Flagged”, this indicates that the email has not yet been reviewed or flagged.
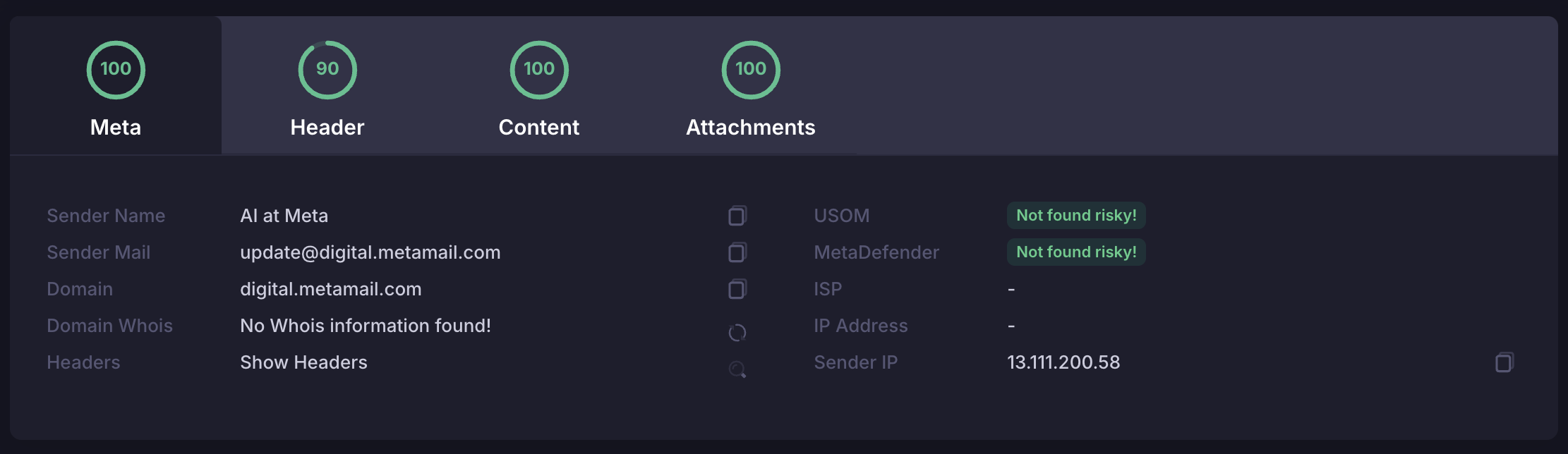
- ℹ️Meta Information: Meta information can include information about the email’s transmission and recipients
-
Title Information:
- 👥CC List: When sending an email, CC refers to contacts who are not the recipients of the email but whom you want to show the email to (To) or other recipients.
- 🕵️♂️BCC List: When sending emails to people on the BCC, their identities or email addresses are hidden to other recipients or others on the BCC list. BCC is useful for ensuring privacy or managing large lists of recipients.
- 📄Content: Shows the content of the email. This section contains links within the email and security evaluation of these links.
- 📎Attachments: May include file attachments within the email or security evaluation of attachments.
- 🏷️Sender Name: Shows the name of the person or organization that sent the email.
- 📧Sender Email: Shows the email address of the person or organization that sent the email.
- 🌐Domain: Shows the domain to which the sender’s email address is connected.
- 📅Domain Registration Date: Shows the registration date of the domain to which the sender’s e-mail address is linked.
- 🌍GeoLocation Info: Contains information about the geographical location where the email was sent.
- 🔗Link: Shows the URL of each link in the email.
- 🔒Protocol: Shows the communication protocol (such as HTTP, HTTPS) used by the link.
- 💻Hostname: Shows the name of the server that the link is targeting.
- 🔌Port: Indicates over which port the connection is made.
- 📂Path: Indicates which path the connection follows on the target server.
- ⚙️Parameters: Shows the parameters in the URL of the connection.
- 🛡️MetaDefender and USOM Information: Contains information that the connection has been scanned or audited by security services such as MetaDefender and USOM.
People in the CC can see that the email has been received and that the content has been viewed, but they are not considered the actual recipient. Typically this is used to inform other people about a topic or to share email messages.
BCC is essentially similar to “CC”, with one difference; the people on the BCC are not visible to other recipients or other people on the BCC list.
